Operating Cost Savings on Data Masking and De-Identification
The prevalent practice in handling PII data is to de-identify the data before processing. This depreciates the quality of derived insights. By processing the data (using secure enclaves) and de-identifying the result reduces the cost of de-identification and improves the quality of insights, all the while remaining HIPAA compliant.
Highly Confidential Exchange Among Agencies and Subcontractors
Privacy and Compliance by Design
Allow only authorized & curated code assets to be brought to your data where they execute on the whole dataset, deriving all the available insights. Cryptography based authorization technology implemented in secure enclaves to achieve trusted enforcements.
New Innovations Bring New Possibilities
Move code assets--while keeping data stationary--across cloud platforms with access being controlled by distributed authorization technology.
Audit and Prove Compliance
Prove compliance with laws and regulations including HIPAA, CCPA, PCI etc. Share advanced auditing tools and reports with regulators to achieve verifiable compliance.
Federated Workflows and HIPAA Compliance
Use SafeLiShare's Federated Workflows to move or receive encrypted data to/from partner organizations without violating HIPAA compliance regulations. Data always remains encrypted until its execution in a secure enclave.
Featured Collateral
CISO’s Guide: Confidential Computing
Confidential Computing is a new-age technology that protects data and computations in use, instead of just protecting data at-rest and in-transit. CISO's guide on Confidential Computing explains how it works through the use of encryption, secure enclaves, data breach life cycle and remediations so organizations can safely protect sensitive user data when stored or processed in the cloud.
Audit-Ready Compliance
- HIPAA/HITECH Compliance
- HITRUST CSF Certification
- SOC 2 Attestation
- FDA GxP Compliance
Expedited Innovations in Treatment and Care
- Data de-identification for accelerated and compliant data access
- Scalable data access for data science and advanced analytics
- Purpose-based restrictions for compliant collaboration
Secure Sensitive Data Sharing with Third Parties
- Share data with contractors, partners, auditors, and other third parties
- Enhance the patient experience
- Improve public health initiatives and trusted outcomes
People also ask
Does HIPAA Apply to Health Insurance?
Should a Life Insurance Company Follow HIPAA Standards?
Are there any privacy concerns associated with mandatory data sharing in the insurance industry?
Additional materials
February 21, 2024
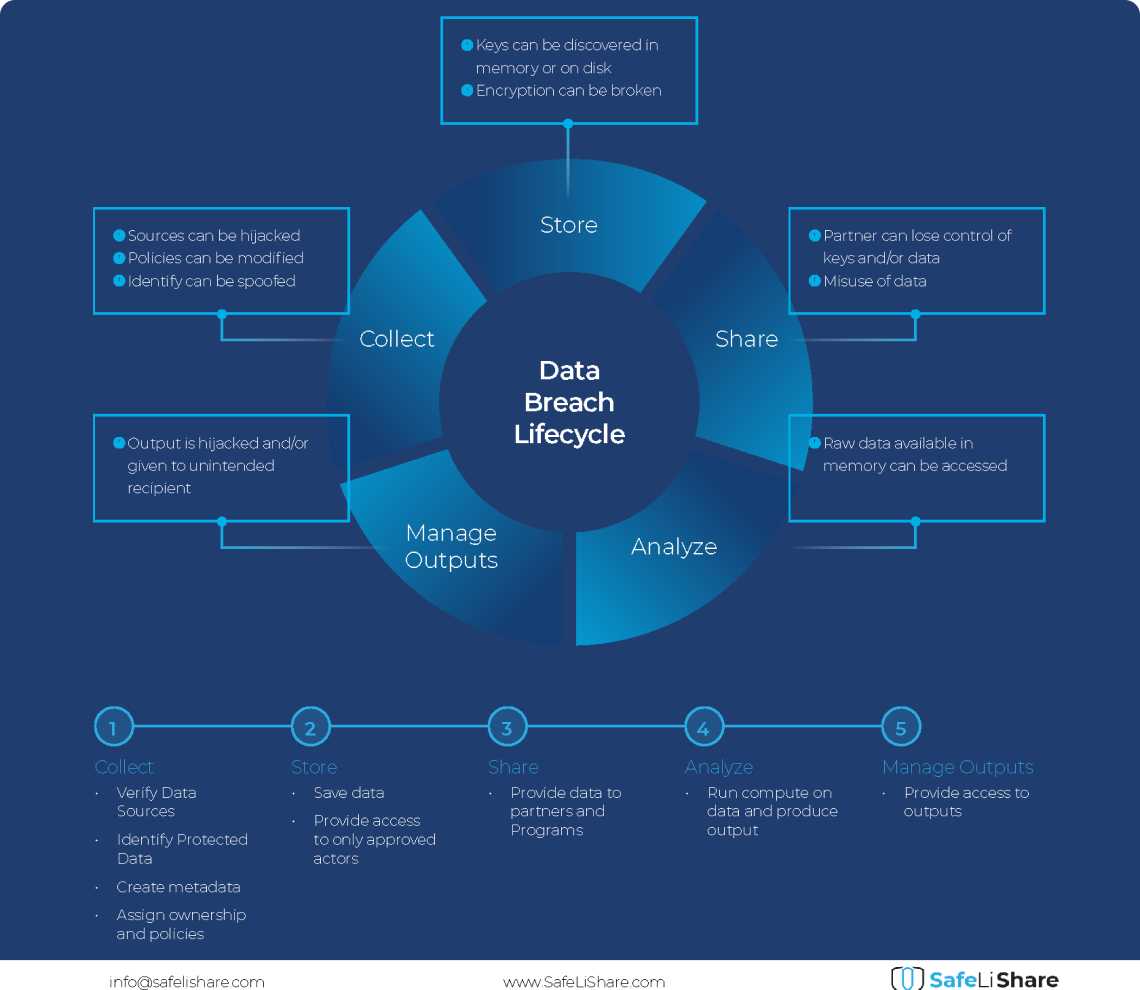
Cloud Data Breach Lifecycle Explained
During the data life cycle, sensitive information may be exposed to vulnerabilities in transfer, storage, and processing activities.

February 21, 2024
Bring Compute to Data
Predicting cloud data egress costs can be a daunting task, often leading to unexpected expenses post-collaboration and inference.
February 21, 2024
Zero Trust and LLM: Better Together
Cloud analytics inference and Zero Trust security principles are synergistic components that significantly enhance data-driven decision-making and cybersecurity resilience.
Experience secure collaborative data sharing today.
Maximize accessibility and monetization of sensitive, regulated, or confidential data without compromise.