Access Controls for Dynamic Applications over Distributed Data
Data sharing is the way to optimize higher-relevant data, generating more robust data and analytics to solve business challenges and meet enterprise goals. Retain controls on who has access to your systems and data as well as what they are able to do with it.
Centralized Multi-Party Distributed Data Access
Centralized Data Access Control
SafeLiShare protects users’ sensitive information by utilizing an isolated and protected Trusted Execution Environment to perform encryption, decryption, authentication, data integrity checks, and other operations to prevent unauthorized access or modification.
Consistent Data Privacy Controls
SafeLiShare uses cryptography to protect user privacy by safeguarding access privilege and control for both applications and users.
Remote Attestation per Data Ownership
SafeLiShare protects against unauthorized modifications and external threats with remote attestation to verify integrity of components.
Ensure Business Continuity with TEE Logging Infrastructure
SafeLiShare’s platform is capable of detecting the tampering of logs both by internal and external adversaries. Internal adversaries are those that may get access to log records when or where they are generated. External adversaries are entities that may get access to records that are persistently stored.
Featured Collateral
CISO’s Guide: Confidential Computing
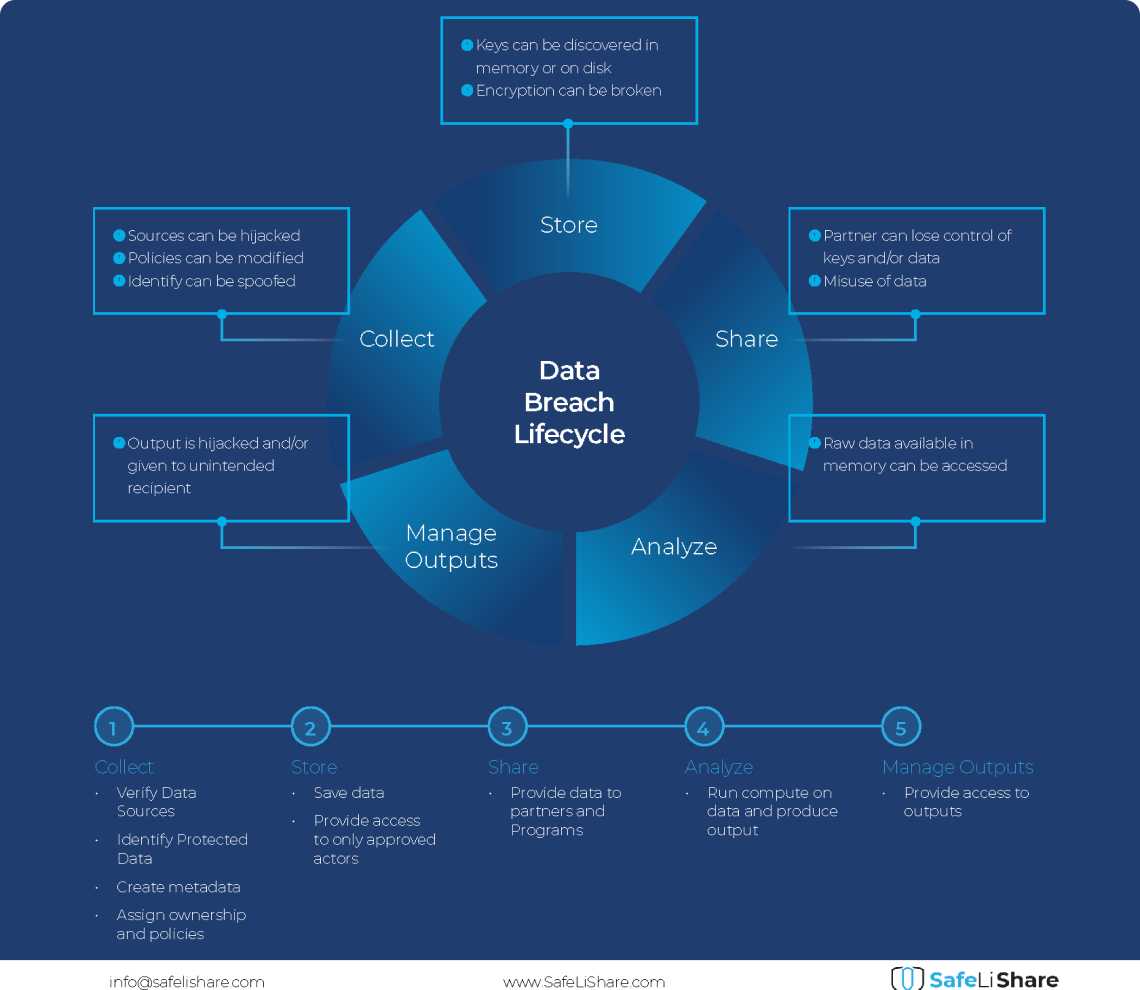
Confidential Computing is a new-age technology that protects data and computations in use, instead of just protecting data at-rest and in-transit. CISO's guide on Confidential Computing explains how it works through the use of encryption, secure enclaves, data breach life cycle and remediations so organizations can safely protect sensitive user data when stored or processed in the cloud.

“SafeLiShare is the manifestation of what people are talking about Confidential Computing. There's a gap between when someone you give access to the environment and how you can enforce what they have access to. So, we can make sure that when someone accesses data, they do so using only programs that we say they can access the data with - the GDPR way.”
Mitch Parker, CISO
Indiana University Health
People also ask
How does distributed access control in secure enclave differ from traditional access control measures?
What type of access data can SafeLiShare provide to fulfill compliance requirements?
What programming languages are supported by the SafeLiShare Confidential Computing solutions?
Additional materials
February 21, 2024
Cloud Data Breach Lifecycle Explained
During the data life cycle, sensitive information may be exposed to vulnerabilities in transfer, storage, and processing activities.

February 21, 2024
Bring Compute to Data
Predicting cloud data egress costs can be a daunting task, often leading to unexpected expenses post-collaboration and inference.
February 21, 2024
Zero Trust and LLM: Better Together
Cloud analytics inference and Zero Trust security principles are synergistic components that significantly enhance data-driven decision-making and cybersecurity resilience.
Experience secure collaborative data sharing today.
Maximize accessibility and monetization of sensitive, regulated, or confidential data without compromise.